Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check_expiration_rdap
Current Version
0.1
Last Release Date
2021-05-26
Compatible With
- Nagios 3.x
Owner
Twitter Handle
buanzo
License
MIT
Hits
3778
Files:
| File | Description |
|---|---|
| nagios_check_domain_expiration_rdap.zip | nagios_check_domain_expiration_rdap.zip |
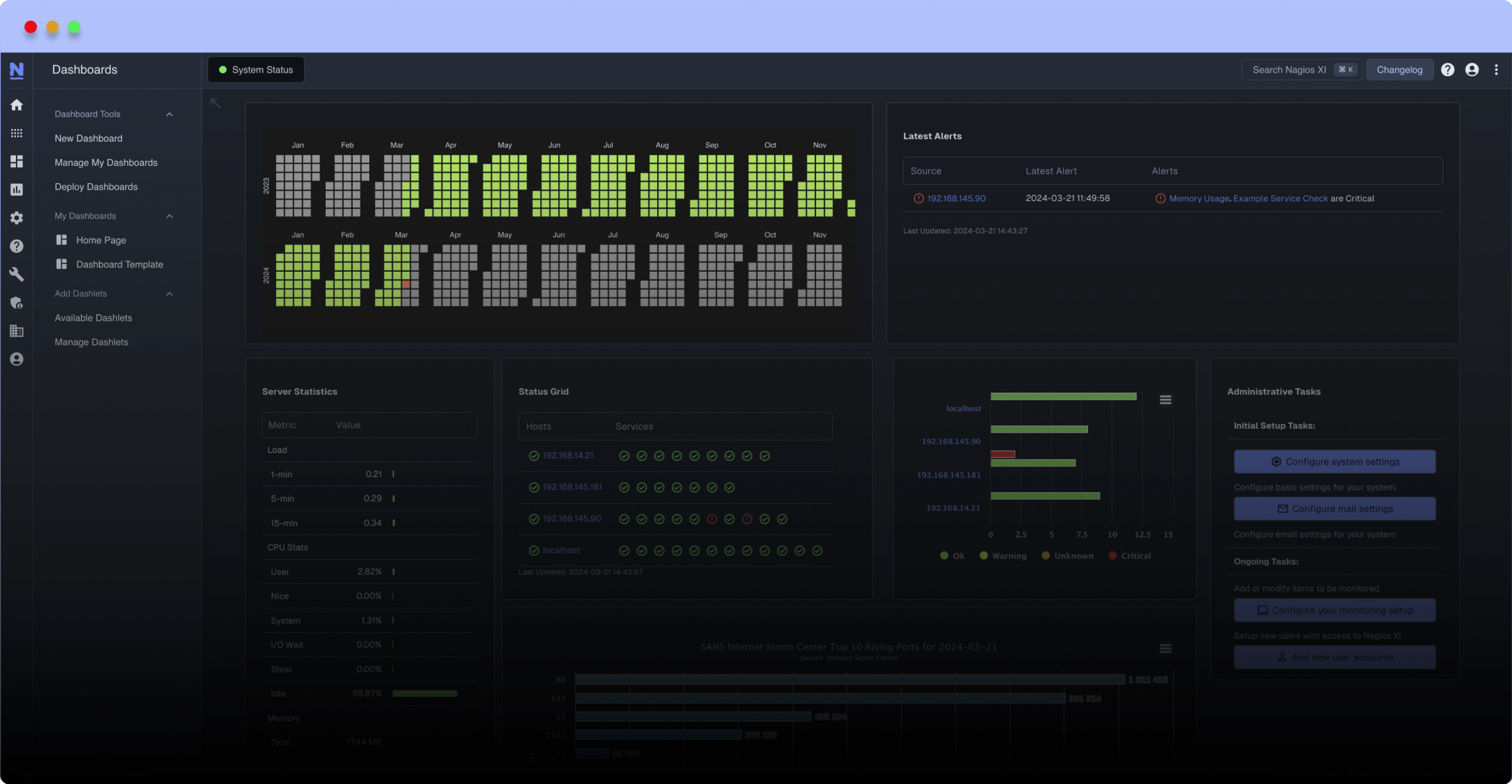
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
Checks how far is a domain from expiring. Uses the Registration Data Access Protocol (RDAP, supporting Bootstrap), does NOT use whois.
INSTALLATION DEPENDENCIES: pip3 install requests nagiosplugin
Works with many ccTLDs such as Argentina. It is compatible with a large number of TLDs. Allows to indicate warning/critical days-to-expiration ranges. By default CRITICAL < 15 days, WARNING < 30 days.
NOTE: I only tested with Nagios 3.x - If someone tests with other versions please let me know. Also, the rdap expiration event timestamp is split at the 'T' marker, thus ignoring time, date or timezone for expiration-today calculation this might introduce an error. I suggest running this plugin with these settings to avoid any potential bans from excessive rdap calls:
define service{
use generic-service
host_name localhost
service_description EXPIRATION example.net
check_command check_rdap_expire!example.net
check_interval 1440 ; Server are checked every 1 day when in OK state
retry_interval 180 ; Server checked every 3 hours if in problem state
max_check_attempts 3 ; Server checked 3 times to determine if its Up or Down state
}
define command{
command_name check_rdap_expire
command_line /usr/local/bin/check_rdap_expire $ARG1$
}
replace example.net and /usr/local/bin/check_rdap_expire according to your installation path.
INSTALLATION DEPENDENCIES: pip3 install requests nagiosplugin
Works with many ccTLDs such as Argentina. It is compatible with a large number of TLDs. Allows to indicate warning/critical days-to-expiration ranges. By default CRITICAL < 15 days, WARNING < 30 days.
NOTE: I only tested with Nagios 3.x - If someone tests with other versions please let me know. Also, the rdap expiration event timestamp is split at the 'T' marker, thus ignoring time, date or timezone for expiration-today calculation this might introduce an error. I suggest running this plugin with these settings to avoid any potential bans from excessive rdap calls:
define service{
use generic-service
host_name localhost
service_description EXPIRATION example.net
check_command check_rdap_expire!example.net
check_interval 1440 ; Server are checked every 1 day when in OK state
retry_interval 180 ; Server checked every 3 hours if in problem state
max_check_attempts 3 ; Server checked 3 times to determine if its Up or Down state
}
define command{
command_name check_rdap_expire
command_line /usr/local/bin/check_rdap_expire $ARG1$
}
replace example.net and /usr/local/bin/check_rdap_expire according to your installation path.
Reviews (0)
Be the first to review this listing!


 New Listings
New Listings