Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
Perl check radius
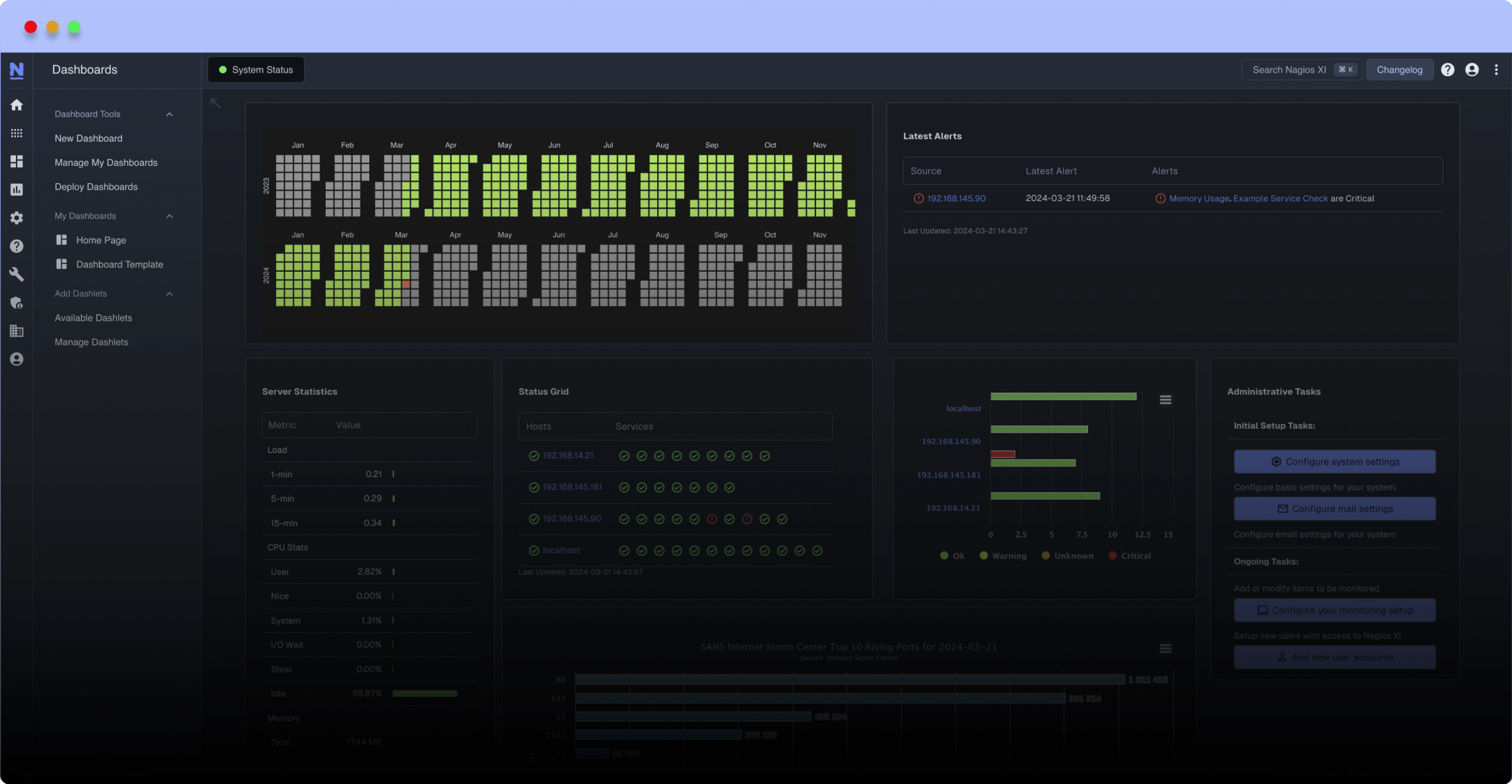
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
# ./check_radius.pl -h
Copyright (C) 2006 Carlos Vicente
Checks if a Radius server can authenticate a username/password
usage: ./check_radius.pl -H host -u username -p password -s secret
[-n nas-ip] [-P port] [-t timeout]
Options:
-h, --help
Print detailed help screen
-H, --hostname=ADDRESS
Host name or IP Address
-P, --port=INTEGER
Port number (default: 1812)
-u, --username=STRING
The user to authenticate
-p, --password=STRING
Password for autentication (SECURITY RISK)
-n, --nas-ip=STRING
NAS IP Address (default: 127.0.0.1)
-s, --secret=STRING
Radius secret
-t, --timeout=INTEGER
Seconds before connection times out (default: 5)
This plugin checks if a username/password can be authenticated against a
Radius Server.
The password option presents a substantial security issue because the
password can be determined by careful watching of the command line in
a process listing. This risk is exacerbated because nagios will
run the plugin at regular predictable intervals. Please make sure that
the password used does not allow access to sensitive system resources,
otherwise, a compromise could occur.
Copyright (C) 2006 Carlos Vicente
Checks if a Radius server can authenticate a username/password
usage: ./check_radius.pl -H host -u username -p password -s secret
[-n nas-ip] [-P port] [-t timeout]
Options:
-h, --help
Print detailed help screen
-H, --hostname=ADDRESS
Host name or IP Address
-P, --port=INTEGER
Port number (default: 1812)
-u, --username=STRING
The user to authenticate
-p, --password=STRING
Password for autentication (SECURITY RISK)
-n, --nas-ip=STRING
NAS IP Address (default: 127.0.0.1)
-s, --secret=STRING
Radius secret
-t, --timeout=INTEGER
Seconds before connection times out (default: 5)
This plugin checks if a username/password can be authenticated against a
Radius Server.
The password option presents a substantial security issue because the
password can be determined by careful watching of the command line in
a process listing. This risk is exacerbated because nagios will
run the plugin at regular predictable intervals. Please make sure that
the password used does not allow access to sensitive system resources,
otherwise, a compromise could occur.
Reviews (5)
byMajed, June 27, 2018
Except would have loved to see the response time... and even perf data
bybatfasturd, October 1, 2015
Authen perl module has some errors, I fixed it by applying this patch.
https://bugs.archlinux.org/task/42132
Now the plugin works just fine.
https://bugs.archlinux.org/task/42132
Now the plugin works just fine.
byventz, November 5, 2013
1 of 1 people found this review helpful
Works very well.
Similar to what we have written in house.
To everyone that has problems, just take out the "-w" flag in the first line of the script (#!/usr/bin/perl)
This flag is for "with warnings", and as advertised -- it displays warnings about the Module you are using (different issue). Either way, it works fine and you need to return back a single word for Nagios -- thus, getting rid of the warnings makes it nagios compatible.
Similar to what we have written in house.
To everyone that has problems, just take out the "-w" flag in the first line of the script (#!/usr/bin/perl)
This flag is for "with warnings", and as advertised -- it displays warnings about the Module you are using (different issue). Either way, it works fine and you need to return back a single word for Nagios -- thus, getting rid of the warnings makes it nagios compatible.
bystruiaj17, September 23, 2013
It appears to be broken on newer versions of Linux. I get this on Ubuntu 11.10:
Use of uninitialized value $vendor_name in hash element at /usr/share/perl5/Authen/Radius.pm line 431
Use of uninitialized value $vendor_name in hash element at /usr/share/perl5/Authen/Radius.pm line 431
byKickstart, July 10, 2012
./check_radius.pl -H servername -u vpntest -p password -s secret
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
CRITICAL
No hint as to what it's looking for or why it is failing.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
Use of uninitialized value in hash element at /usr/lib/perl5/site_perl/5.8.8/Authen/Radius.pm line 432.
CRITICAL
No hint as to what it's looking for or why it is failing.


 New Listings
New Listings