Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check radius adv
Owner
Hits
110314
Files:
| File | Description |
|---|---|
| samplefile.txt | A sample attributes file |
| check_radius_adv_2006_08_23.tar.gz | The plugin |
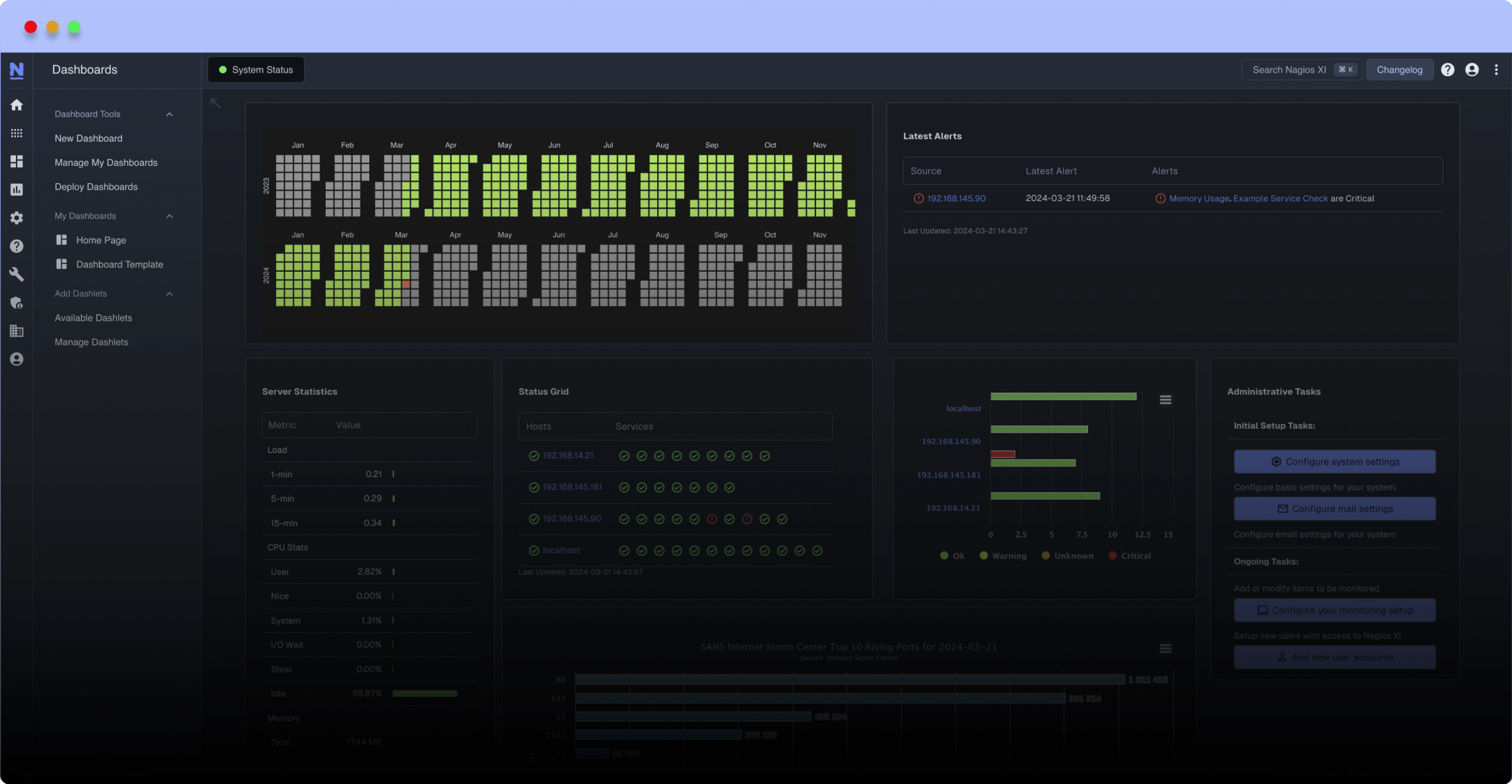
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
Advanced features
The advanced featetures compared to original check_radius are:
* radius attributes used for the authentication can be defined.
* command paramater for which radius reply ends in an ok state
* command parameter to check the Reply-Msg from the radius server
Installation
Just unpack the file. And afterwards use ./configure and make
Usage
check_radius_adv
Usage: # ./check_radius_adv OPTIONS...
OPTIONS
-v verbose (output with verification)
-u [username] cleartext username
-p [password] cleartext password
-s [shared secret] shared secret for RADIUS server
-r [radius server] radius server to auth
-c [radius port] radius server port (default: 1812)
-t [auth timeout] interval to wait until auth timeout in seconds (default: 30 sec.)
-a [attributes] filename of the attributes file (see samplefile)
-o [ok state] auth reply code which will return ok state (default: 2 = accepted)
-e [error code] plugin error-code in case reply code differs (default: 2 = critical)
-m [replymsg] expected replymsg (type=18) (default: "")
-h this menu
Additional Attributes
You can add Strings, Integers, Addresses and Times. But please, check the attached samplefile
Credits
This plugin was kindly sponsored by T-Mobile
Changelog
* **2006-03-22** Parameters with hexvalues (e.g. /x3B for a semicolon) as patterns are translated into their ascii characters. //That is why / has also be escaped as ``//``//.
* failure was not recognize if length of replymsg was longer than the expected
* **2006-08-23** Corrected string handling - changed c-style strings to rfc-conform strings. Parameters with /x00 did not work correctly.
The advanced featetures compared to original check_radius are:
* radius attributes used for the authentication can be defined.
* command paramater for which radius reply ends in an ok state
* command parameter to check the Reply-Msg from the radius server
Installation
Just unpack the file. And afterwards use ./configure and make
Usage
check_radius_adv
Usage: # ./check_radius_adv OPTIONS...
OPTIONS
-v verbose (output with verification)
-u [username] cleartext username
-p [password] cleartext password
-s [shared secret] shared secret for RADIUS server
-r [radius server] radius server to auth
-c [radius port] radius server port (default: 1812)
-t [auth timeout] interval to wait until auth timeout in seconds (default: 30 sec.)
-a [attributes] filename of the attributes file (see samplefile)
-o [ok state] auth reply code which will return ok state (default: 2 = accepted)
-e [error code] plugin error-code in case reply code differs (default: 2 = critical)
-m [replymsg] expected replymsg (type=18) (default: "")
-h this menu
Additional Attributes
You can add Strings, Integers, Addresses and Times. But please, check the attached samplefile
Credits
This plugin was kindly sponsored by T-Mobile
Changelog
* **2006-03-22** Parameters with hexvalues (e.g. /x3B for a semicolon) as patterns are translated into their ascii characters. //That is why / has also be escaped as ``//``//.
* failure was not recognize if length of replymsg was longer than the expected
* **2006-08-23** Corrected string handling - changed c-style strings to rfc-conform strings. Parameters with /x00 did not work correctly.
Reviews (3)
byhavrla, July 5, 2016
Heloo
ERROR:
[root@paklic plugins]# ./check_radius_adv -u info@itnaklic.cz -p infousek -s radiusheslo -r 10.27.24.4
WARNING: Reply-Msg differs! ('' != '?F??F??????????F') Access ACCEPT. (code = 2) | rtt=0.0029 rttms=2.9079
:D :D :D :
[root@paklic plugins]# ./check_radius_adv -u info@itnaklic.cz -p infousek -s radiusheslo -r 10.27.24.4 -O
./check_radius_adv: invalid option -- 'O'
OK: Access ACCEPT. (code = 2) | rtt=0.0037 rttms=3.6969
[root@paklic plugins]#
OK:
[root@paklic plugins]# ./check_radius_ih -u info@itnaklic.cz -p infousek -s radiusheslo -r 10.27.24.4
OK: Access GRANTED. (code = 2) | rtt=0.0027 rttms=2.7389
[root@paklic plugins]#
Havrla
ERROR:
[root@paklic plugins]# ./check_radius_adv -u info@itnaklic.cz -p infousek -s radiusheslo -r 10.27.24.4
WARNING: Reply-Msg differs! ('' != '?F??F??????????F') Access ACCEPT. (code = 2) | rtt=0.0029 rttms=2.9079
:D :D :D :
[root@paklic plugins]# ./check_radius_adv -u info@itnaklic.cz -p infousek -s radiusheslo -r 10.27.24.4 -O
./check_radius_adv: invalid option -- 'O'
OK: Access ACCEPT. (code = 2) | rtt=0.0037 rttms=3.6969
[root@paklic plugins]#
OK:
[root@paklic plugins]# ./check_radius_ih -u info@itnaklic.cz -p infousek -s radiusheslo -r 10.27.24.4
OK: Access GRANTED. (code = 2) | rtt=0.0027 rttms=2.7389
[root@paklic plugins]#
Havrla
bydrawkcab, October 15, 2010
I can also attest to tguthmann's experience, with approximately 1% of tests failing because the hash is sent blank.
tguthmann, could you publish the patch file in full ? it seems the site has trimmed the code. We are eager to try the patched version!
tguthmann, could you publish the patch file in full ? it seems the site has trimmed the code. We are eager to try the patched version!
bytguthmann, September 8, 2010
Hi,
Just a comment to say this plugin is great and easier to use than check_radius. However, we found a bug which happen once in a while (~1% of the time). The hash is empty. Indeed hash=0000000000000000. Why I really don't known...
After adding more debug, I found the bug in this loop of fnGeneratePasswordHash:
/* as long as the cipher block is valid, concatenate it onto our hash
* password
*/
(while ((x rors by doing that. So if someone, smarter than me can fix this with more elegance. Feel free. In the mean time, applying the following patch assure that over 100k tests in a row, you don't have any errors like we had before.
Thomas
----snip----snip-----
--- check_radius_adv.c.ORI 2010-09-09 18:09:55.258325002 +1000
+++ check_radius_adv.c 2010-09-09 18:13:17.435608325 +1000
@@ -580,7 +580,7 @@
int fnGeneratePasswordHash(RADIUS_HEADER *radhead)
{
- unsigned char b[8][16], p[8][16], c[8][16];
+ unsigned char b[8][16], p[8][16], c[8][16], hash[128];
unsigned char ssra[49];
int currlen = 0, pwlen = global.password.pw_clear[0], bpos = 0, ppos = 0, cpos = 0, x, sslen;
@@ -588,6 +588,7 @@
memset(b,0,128);
memset(p,0,128);
memset(c,0,128);
+ memset(hash,0,128);
memset(ssra,0,49);
sslen = global.sharedsecret[0];
@@ -631,8 +632,10 @@
/* from 0 to 16, XOR the clear text password with the hashed
* md5 output
*/
- for (x = 0; x
Just a comment to say this plugin is great and easier to use than check_radius. However, we found a bug which happen once in a while (~1% of the time). The hash is empty. Indeed hash=0000000000000000. Why I really don't known...
After adding more debug, I found the bug in this loop of fnGeneratePasswordHash:
/* as long as the cipher block is valid, concatenate it onto our hash
* password
*/
(while ((x rors by doing that. So if someone, smarter than me can fix this with more elegance. Feel free. In the mean time, applying the following patch assure that over 100k tests in a row, you don't have any errors like we had before.
Thomas
----snip----snip-----
--- check_radius_adv.c.ORI 2010-09-09 18:09:55.258325002 +1000
+++ check_radius_adv.c 2010-09-09 18:13:17.435608325 +1000
@@ -580,7 +580,7 @@
int fnGeneratePasswordHash(RADIUS_HEADER *radhead)
{
- unsigned char b[8][16], p[8][16], c[8][16];
+ unsigned char b[8][16], p[8][16], c[8][16], hash[128];
unsigned char ssra[49];
int currlen = 0, pwlen = global.password.pw_clear[0], bpos = 0, ppos = 0, cpos = 0, x, sslen;
@@ -588,6 +588,7 @@
memset(b,0,128);
memset(p,0,128);
memset(c,0,128);
+ memset(hash,0,128);
memset(ssra,0,49);
sslen = global.sharedsecret[0];
@@ -631,8 +632,10 @@
/* from 0 to 16, XOR the clear text password with the hashed
* md5 output
*/
- for (x = 0; x


 New Listings
New Listings