Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check_portaudit
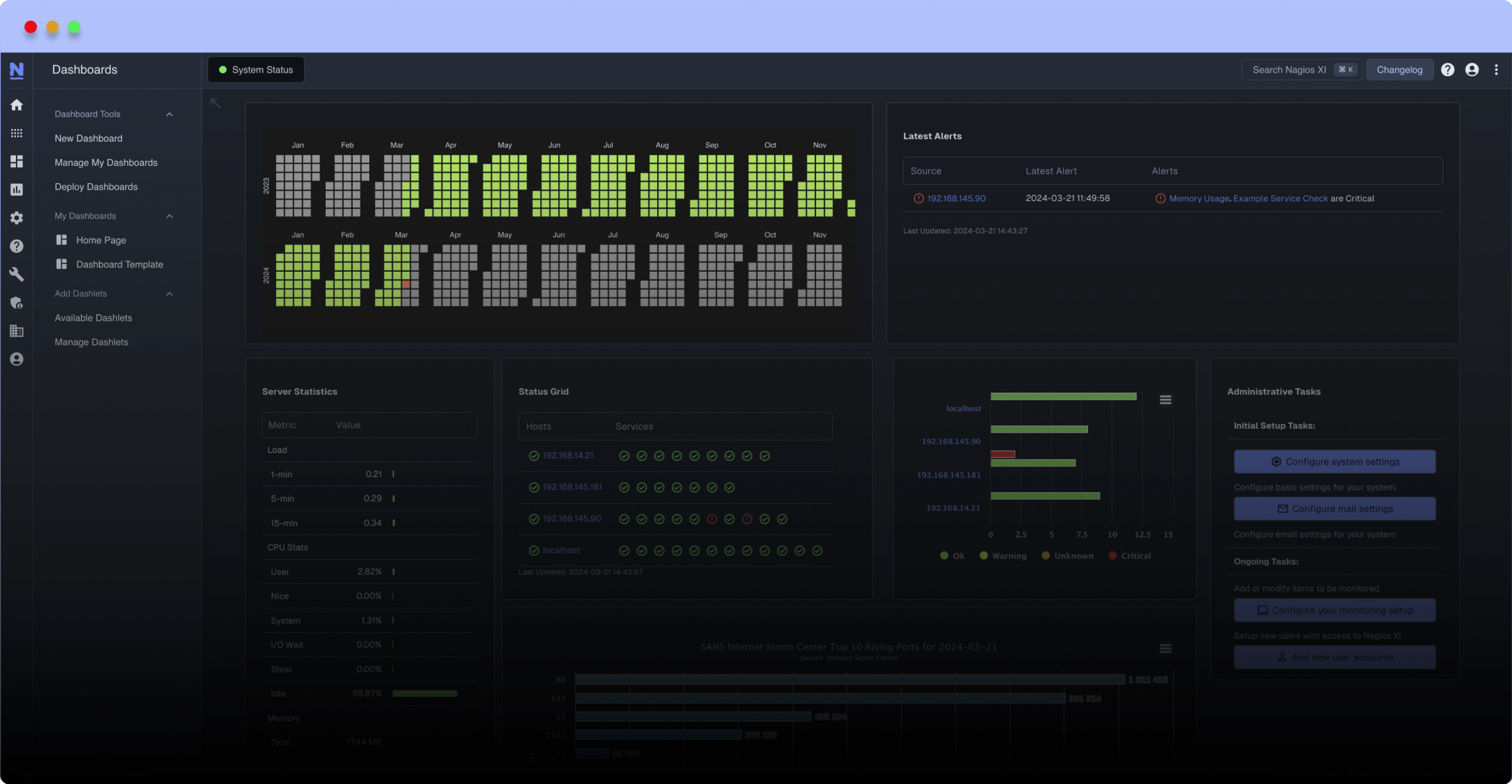
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
This plugin relies on portaudit and/or portupgrade packages to be installed on your FreeBSD system. With these packages installed, the plugin will scan your system for either vulnerable packages, or obsolete packages - and display appropriate warnings to Nagios.
Portaudit can also be successfully run remotely from nrpe, and does not require superuser privileges to operate.
Usage: check_portaudit (security/updates) (show/noshow) database age limit (days)
Example: check_portaudit security show 3
COMMANDS
security - run portaudit and displays vulnerable packages. (Requires "portaudit" installation.)
updates - runs portversion and lists packages which need updating. (Requires "portupgrade" installation.)
You can choose whether to show or not show vulnerable/old packages by name. The message line may be incredibly huge if you have a lot of old/vulnerable packages, so using "noshow" you are guaranteed a single line of text.
DISPLAY
show - shows all packages by name when vulnerable/obsolete packages detected
noshow - do not show package names. Simply display number of packages detected
DATABASE AGE LIMIT
The database age limit option will produce CRITICAL errors by default if either the portaudit database or the ports tree is older than a certain number of days. If this argument is not specified, the default will be 7 days.
WARNINGS will be delivered should old/vulnerable packages be discovered otherwise you will get an OK result.
It is STRONGLY recommended that you update your ports database to maintain accurate information. A cronjob will easily accomplish this as superuser. A portaudit install will automatically add a periodic cronjob to update its database - and assuming an ever present internet connection, you won't need to worry about updating it.
Updating portsdb (in addition to syncing the ports tree) :-
# portsdb -Fu
Updating portaudit manually:-
# portaudit -F
Portaudit can also be successfully run remotely from nrpe, and does not require superuser privileges to operate.
Usage: check_portaudit (security/updates) (show/noshow) database age limit (days)
Example: check_portaudit security show 3
COMMANDS
security - run portaudit and displays vulnerable packages. (Requires "portaudit" installation.)
updates - runs portversion and lists packages which need updating. (Requires "portupgrade" installation.)
You can choose whether to show or not show vulnerable/old packages by name. The message line may be incredibly huge if you have a lot of old/vulnerable packages, so using "noshow" you are guaranteed a single line of text.
DISPLAY
show - shows all packages by name when vulnerable/obsolete packages detected
noshow - do not show package names. Simply display number of packages detected
DATABASE AGE LIMIT
The database age limit option will produce CRITICAL errors by default if either the portaudit database or the ports tree is older than a certain number of days. If this argument is not specified, the default will be 7 days.
WARNINGS will be delivered should old/vulnerable packages be discovered otherwise you will get an OK result.
It is STRONGLY recommended that you update your ports database to maintain accurate information. A cronjob will easily accomplish this as superuser. A portaudit install will automatically add a periodic cronjob to update its database - and assuming an ever present internet connection, you won't need to worry about updating it.
Updating portsdb (in addition to syncing the ports tree) :-
# portsdb -Fu
Updating portaudit manually:-
# portaudit -F
Reviews (1)
bySimerson, August 27, 2014
The old pkg_ tools are no longer maintained and this script doesn't work with pkgng. I have an updated version here: http://www.tnpi.net/computing/freebsd/check_portaudit.pl


 New Listings
New Listings