Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check_bundle_audit
Current Version
0.6.0
Last Release Date
2017-10-29
Compatible With
- Nagios 1.x
- Nagios 2.x
- Nagios 3.x
Owner
Download URL
License
MIT
Hits
7738
Files:
| File | Description |
|---|---|
| check_bundle_audit.sh | check_bundle_audit.sh |
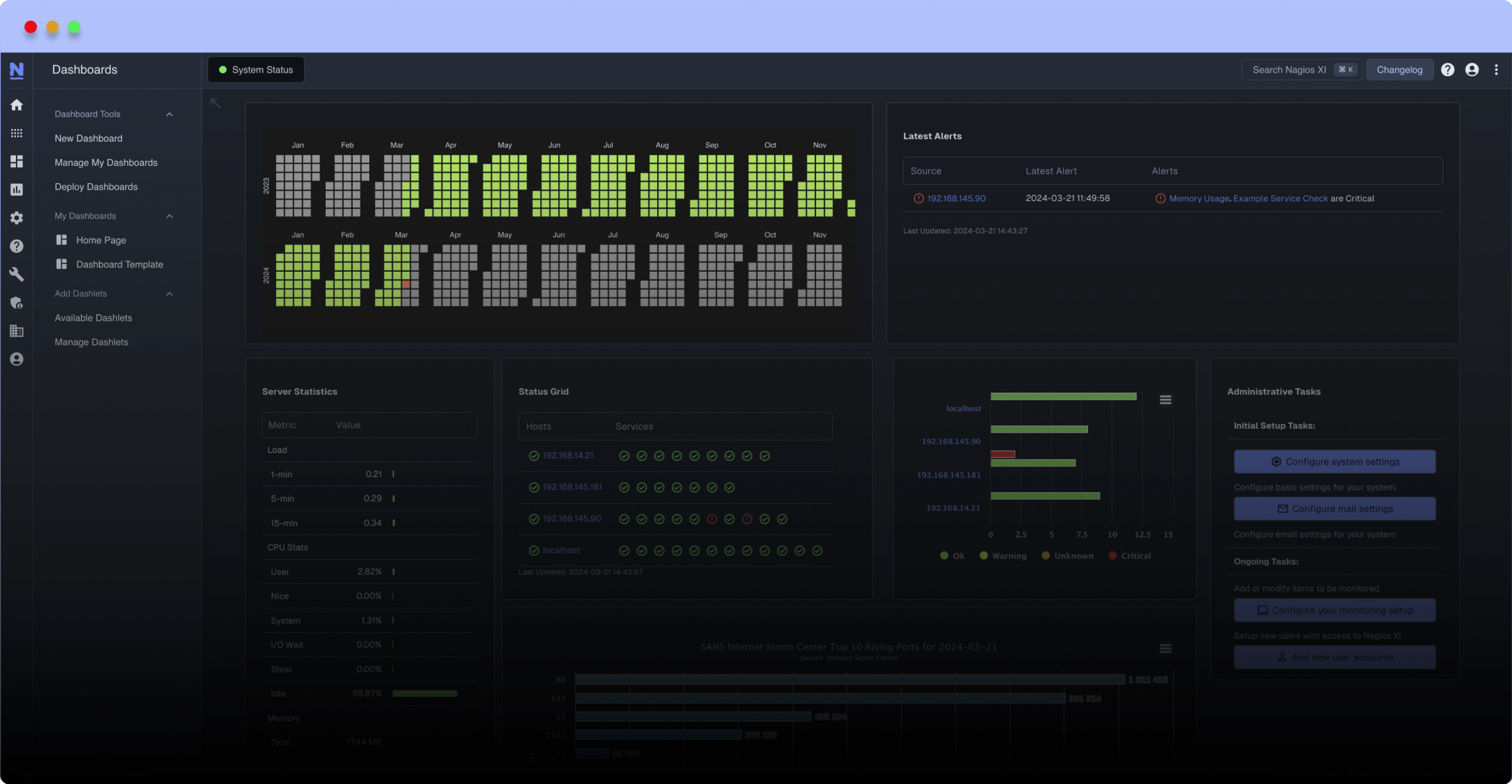
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
Nagios plugin to monitor ruby applications for security vulnerabilities via bundler-audit.
Usage:
./check_bundle_audit -p [options]
Examples:
# 'Unknown' or 'High' CVEs exit CRITICAL; 'Medium' or 'Low' exit WARNING
./check_bundle_audit -p /var/www/app
# exit CRITICAL if any CVE(s) are present
./check_bundle_audit -p /var/www/app -c all
# exit WARNING if any CVE(s) (including high) are present
./check_bundle_audit -p /var/www/app -c '' -w all
# 'High' CVEs exit CRITICAL; 'Unknown' or 'Medium' exit WARNING; 'Low' exit OK
./check_bundle_audit -p /var/www/app -c high -w medium,unknown
# 'High' CVEs exit CRITICAL; 'Medium', 'Low' or 'Unknown' exit WARNING
./check_bundle_audit -p /var/www/app -c high -w medium,low,unknown
# set full path to bundle-audit
./check_bundle_audit -p /var/www/app -b /usr/local/bin/bundle-audit
# ignore advisories CVE-2016-4658 and CVE-2014-0083
./check_bundle_audit -p /var/www/app -i "CVE-2016-4658 CVE-2014-0083"
Options:
-p, --path path to project
-b --bundle-audit-path path to `bundle-audit` gem
-w, --warning comma seperated CVE criticalities to treat as WARNING
-c, --critical comma seperated CVE criticalities to treat as CRITICAL
-i, --ignore space seperated advisories to ignore
-V, --version output version
-h, --help output help information
Criticalities:
* -c/--critical takes priority over -w/--warning.
* -c/--critical default is high,unknown.
* -w/--warning default is low,medium,high,unknown.
* Criticality levels:
- low
- medium
- high
- unknown
- all (alias for low,medium,high,unknown)
Troubleshooting:
UNKNOWN: Unable to update ruby-advisory-db
bundler-audit downloads a copy of the Ruby Advisory Database inside the user's home directory. This can cause issues if the user running the script does not have a writable home directory. See https://github.com/tommarshall/nagios-check-bundle-audit/issues/2 for details on how to resolve this.
Dependencies:
* bash
* bundler-audit (https://github.com/rubysec/bundler-audit)
Usage:
./check_bundle_audit -p
Examples:
# 'Unknown' or 'High' CVEs exit CRITICAL; 'Medium' or 'Low' exit WARNING
./check_bundle_audit -p /var/www/app
# exit CRITICAL if any CVE(s) are present
./check_bundle_audit -p /var/www/app -c all
# exit WARNING if any CVE(s) (including high) are present
./check_bundle_audit -p /var/www/app -c '' -w all
# 'High' CVEs exit CRITICAL; 'Unknown' or 'Medium' exit WARNING; 'Low' exit OK
./check_bundle_audit -p /var/www/app -c high -w medium,unknown
# 'High' CVEs exit CRITICAL; 'Medium', 'Low' or 'Unknown' exit WARNING
./check_bundle_audit -p /var/www/app -c high -w medium,low,unknown
# set full path to bundle-audit
./check_bundle_audit -p /var/www/app -b /usr/local/bin/bundle-audit
# ignore advisories CVE-2016-4658 and CVE-2014-0083
./check_bundle_audit -p /var/www/app -i "CVE-2016-4658 CVE-2014-0083"
Options:
-p, --path
-b --bundle-audit-path path to `bundle-audit` gem
-w, --warning
-c, --critical
-i, --ignore
-V, --version output version
-h, --help output help information
Criticalities:
* -c/--critical takes priority over -w/--warning.
* -c/--critical default is high,unknown.
* -w/--warning default is low,medium,high,unknown.
* Criticality levels:
- low
- medium
- high
- unknown
- all (alias for low,medium,high,unknown)
Troubleshooting:
UNKNOWN: Unable to update ruby-advisory-db
bundler-audit downloads a copy of the Ruby Advisory Database inside the user's home directory. This can cause issues if the user running the script does not have a writable home directory. See https://github.com/tommarshall/nagios-check-bundle-audit/issues/2 for details on how to resolve this.
Dependencies:
* bash
* bundler-audit (https://github.com/rubysec/bundler-audit)
Reviews (0)
Be the first to review this listing!


 New Listings
New Listings