Search Exchange
Search All Sites
Nagios Live Webinars
Let our experts show you how Nagios can help your organization.Login
Directory Tree
check_ddos
Current Version
1
Last Release Date
2017-03-19
Compatible With
- Nagios 3.x
- Nagios 4.x
Owner
Twitter Handle
@chipongue04
License
GPL
Hits
8622
Files:
| File | Description |
|---|---|
| check_ddos.py | check_ddos.py |
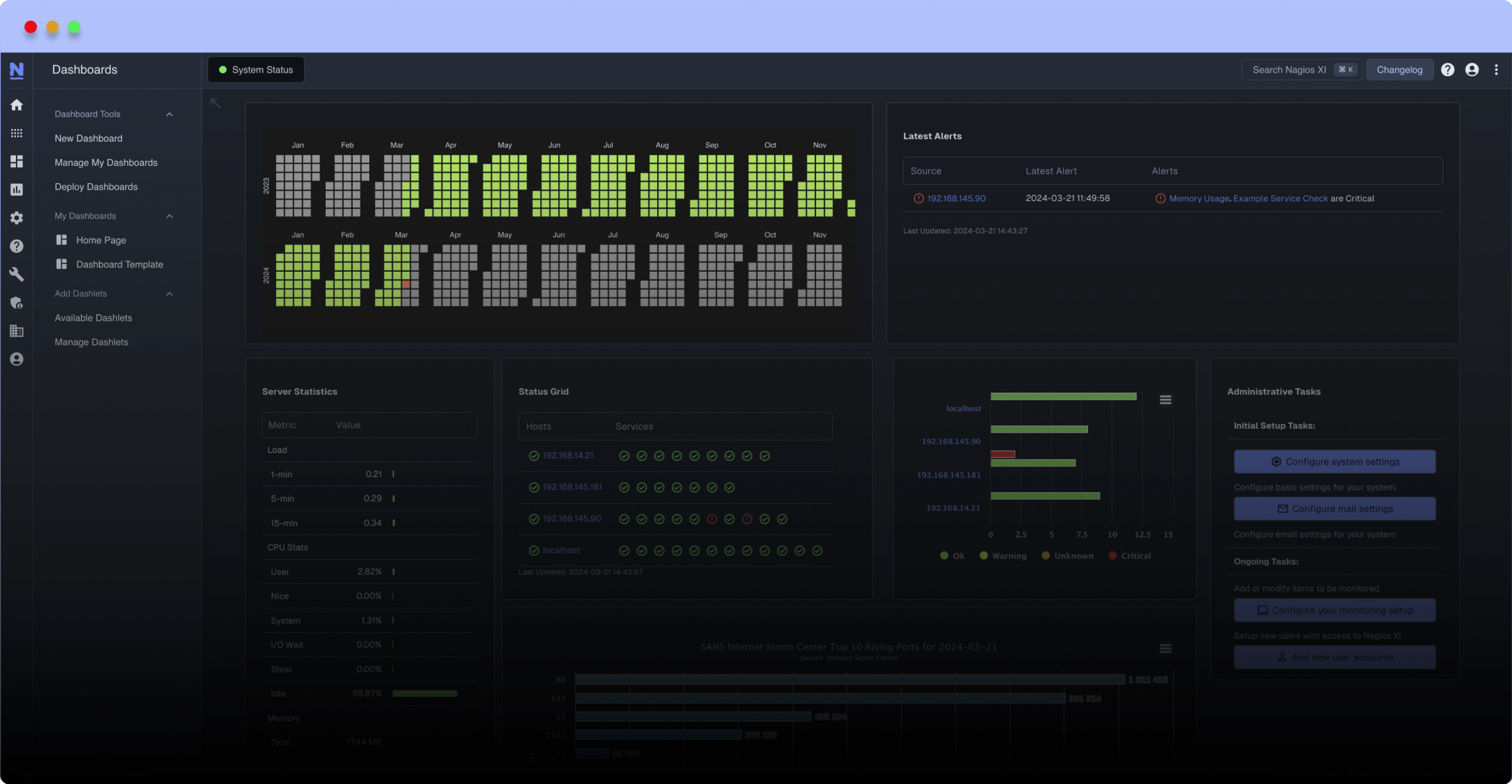
Meet The New Nagios Core Services Platform
Built on over 25 years of monitoring experience, the Nagios Core Services Platform provides insightful monitoring dashboards, time-saving monitoring wizards, and unmatched ease of use. Use it for free indefinitely.
Monitoring Made Magically Better
- Nagios Core on Overdrive
- Powerful Monitoring Dashboards
- Time-Saving Configuration Wizards
- Open Source Powered Monitoring On Steroids
- And So Much More!
Monitoring of DDoS
SYN flood attacks is a type of denial of service or distributed denial of service (DDoS) attack, which consists of direct overhead in the transport layer and indirect in the application layer of the OSI target system model with a sequence of SYN requisitions. Despite the DOS or DDoS attacks do not compromise systems with intrusions or infections with viruses They aim to make services and/or systems unavailable, generating financial losses or reputation damages.
This Nagios plugin monitors system network connections alerting whenever a large number of SYN recv states are verified. The quantities of connections to be considered excessive are passed as arguments, and when Nagios is exceeded alert with the states warning or critical.
Mandatory arguments: The following arguments must be specified when the module is executed:
-w or warning used to specify the number of connections from which to consider as warning.
-c or critical used to specify the number of connections from which the result should be considered as critical.
Optional arguments: The following arguments are optionally invoked, as user needs:
-V or – version used to query the module version.
-A or – author used to query the author's data.
Command-Line Execution example:
./check_ddos.py -c 300 -w 200
SYN flood attacks is a type of denial of service or distributed denial of service (DDoS) attack, which consists of direct overhead in the transport layer and indirect in the application layer of the OSI target system model with a sequence of SYN requisitions. Despite the DOS or DDoS attacks do not compromise systems with intrusions or infections with viruses They aim to make services and/or systems unavailable, generating financial losses or reputation damages.
This Nagios plugin monitors system network connections alerting whenever a large number of SYN recv states are verified. The quantities of connections to be considered excessive are passed as arguments, and when Nagios is exceeded alert with the states warning or critical.
Mandatory arguments: The following arguments must be specified when the module is executed:
-w or warning used to specify the number of connections from which to consider as warning.
-c or critical used to specify the number of connections from which the result should be considered as critical.
Optional arguments: The following arguments are optionally invoked, as user needs:
-V or – version used to query the module version.
-A or – author used to query the author's data.
Command-Line Execution example:
./check_ddos.py -c 300 -w 200
Reviews (0)
Be the first to review this listing!


 New Listings
New Listings